As the world becomes more encrypted, packets still hold the key for data breach investigations, but in new ways that look at packet metadata instead of the actual packet content. Breaking and inspecting with decryption keys, middleboxes, or endpoints presents performance and privacy challenges.
But packets can still unlock powerful clues to detect and reconstruct timelines of cyberattacks even while encrypted. LiveAction uses a technique called encrypted traffic analysis or ETA that relies on three levels of packet data to make inferences about what is going on inside the flow.
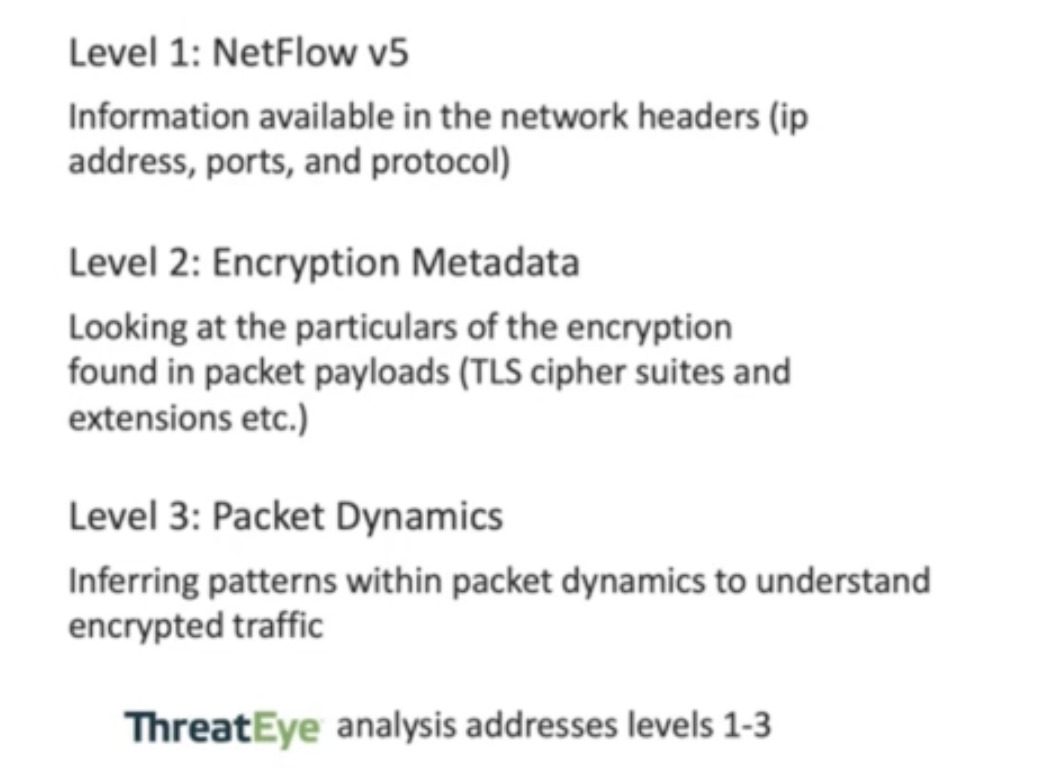
Three different levels of rich data you can get out of your packet.
1. The header information or NetFlow v5
See when a host is talking to someone else, the source IPs, destination IPs, the source ports, destination ports, protocols used, bytes in packets, timing and duration, and the type of connection between these two parties without the payloads.
2. Metadata from the encryption
Encrypted Metadata Analytics looks at certificates and parameters, and the observer can analyze characteristics of the communication channel itself, such as the cipher strength and type, server identification, and whether a connection has been downgraded or not. All of those characteristics are available. It provides security by combining crypto analysis techniques with traditional traffic analysis and machine learning to detect complex patterns within that connection.
3. Packet dynamics
Packet dynamics is data describing packet features. It observes the size of packets, the interarrival time, and the relationship between those sizes and arrival times between different types of connections to make inferences about the content without being able to see the payload.
All of these data sources provide visibility without decrypting the payload. Let’s look at how packets can help you identify attacker behavior and common cyber attacks.
Brute Force Attempts
When taking on brute force attempts, we are looking to detect applications like remote service usage and how often someone connects to RDP or SSH. We investigate how many bytes and packets are involved in those remote connections, what file transfers are being made, and to whom those files are being transferred. Other information collected includes new links on new adjacent hosts and file transfers. The baseline indicators of this attack include scanning, significant binary transfer, and replications of behavior indicating malware infections are spreading.
Both RDP and SSH have multiple handshakes. Depending on the packets in those handshakes, we can detect whether it’s successful or a failure. If a brute force attempt happens, the ability to reference this historical packet data of successful or failed connections across different flows can point to when initial access occurs. In action, the scenario might play out this way: you fail your password too many times, that IP is flagged, and a successful connection from that IP is made.
This visibility allows IT teams to create targeted alerts with a higher priority for these situations. While packet dynamics cannot see user names or passwords, the metadata reveals the reactive behavior of the system as it responds to successful or failed attempts.
Phishing Attacks
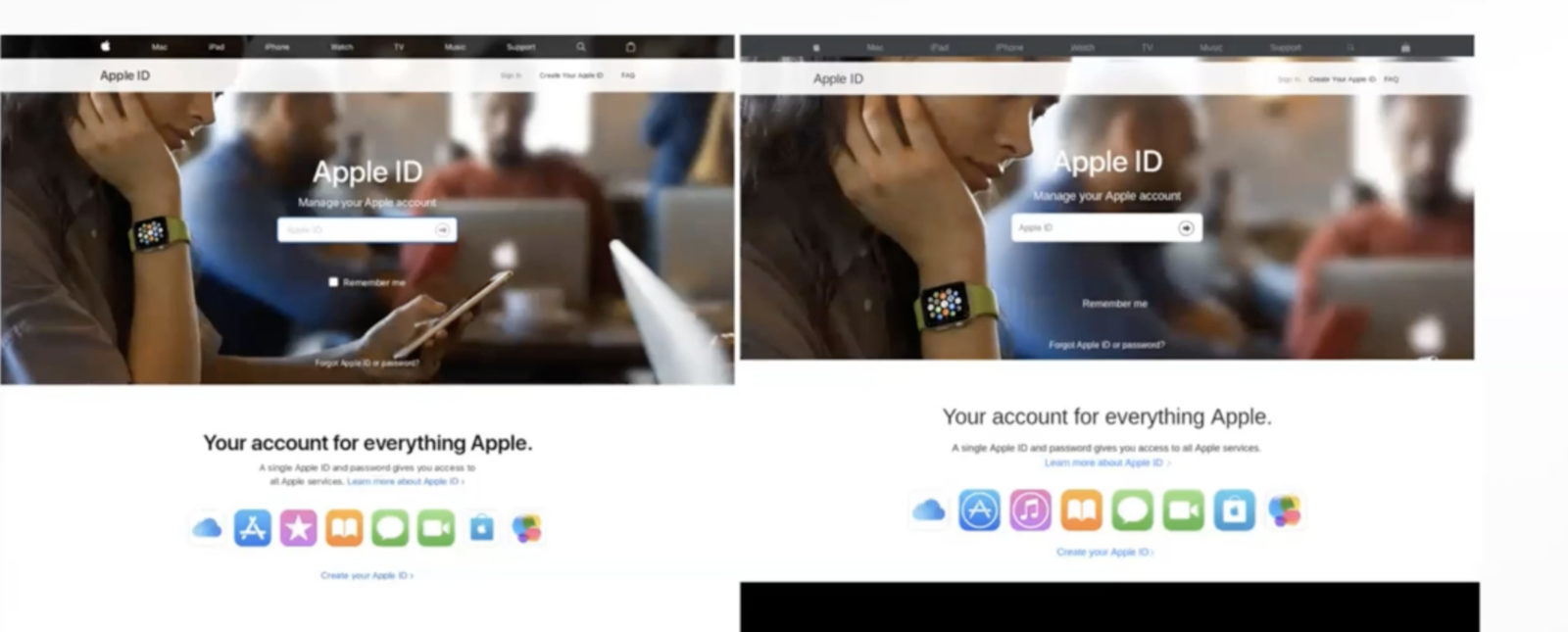
Packet dynamics plus machine learning can help end-users detect phishing attempts. Many phishing schemes are based on URLs and domains, with people clicking on phishing emails. Our approach looks at the web traffic coming in. The packet dynamic signature of phishing websites is detectably different from most traditional websites on the internet. Because of this, a packet dynamic driven ML model can differentiate between the two. This model is built by collecting and comparing thousands of examples of known phishing sites that have been human validated against known secure websites.
Near matches for Facebook or banks pixel for a pixel are impossible to tell apart from the human eye. Machine learning looks at the packet dynamics and the differences in arrival time, different patterns of downloads, and keyboard interactions. LiveAction created a supervised model that trains on known phishing data and gets applied to new data as it comes in, looking for detection.
Command and Control Attacks (C2)
Look for unexpected encryption in the bytes to indicate a Command and Control Attack. A Command and Control attack might try to take advantage of open and existing ports like Port 80, traditionally unencrypted HTTP traditionally open on most firewalls. If a particular malware uses encrypted command and control, it may use Port 80. We look for characteristic entropy scores for specific protocols that can help detect whether this is operating as intended.
Port 443 is typically an encrypted port corresponding to HTTPS. Most web traffic goes over port 443 today, but because it’s open to the firewall, some malware also uses it – trick bot malware can send plain text HTTP over 443. Overall we are looking for encryption in the wrong places and plain text when it should be encrypted and can detect these anomalies using packet dynamics.
Identifying Threat Actor Behavior
Reconnaissance
An infected host will search for vulnerable hosts in the network using active or passive scanning. PCAP allows you to look for unique hosts, an unusual number of hosts, port scanned, IP scanned
Lateral Movement
Lateral movement begins when data is transferred to the vulnerable host. The file or malware is configured, and the next host becomes infected, repeating the behavior to a new host. We look for compound, repeated behavior in packet dynamics to identify this movement.
Data Collection
Valuable data is transferred and concentrated at specific hosts in preparation for exfiltration. This is usually executed at a “low and slow” pace to avoid detection. The infected hosts will reach out to other infected hosts and pull data to a staging point for exfiltration. Changing trends over time can be identified by metrics like the number of packets, bytes, file transfers, application usage, and data sent between hosts. These results can reveal data staging for exfiltration.
Exfiltration
Exfiltration happens when staged data is exported to an external party outside the network. Threat actors often send data to outside hosts using standard and custom communication channels. How the host behaves over time can be identified by looking at packets, bytes, how many domains are accessed, and how many bytes are sent to each domain. Change points in the daily transfers may not exceed an individual threshold, but over time they will Packet metadata analytics to alert organizations to exfiltration in action and when likely indicators are present.
About LiveAction
LiveAction provides unmatched visibility into network and application performance from a single pane of glass. This gives enterprises confidence that the network is meeting business objectives, offers IT administrators full visibility for better decision-making, and reduces the overall cost of operations. By unifying and simplifying the collection, correlation and presentation of network and application data, LiveAction empowers network and security professionals to proactively and quickly identify, troubleshoot, and resolve issues across increasingly large and complex networks. To learn more and see how LiveAction delivers unmatched network visibility and security, visit https://www.liveaction.com.