ThreatEye
Network Detection and Response.
Uncover cyber threats, without decryption, by ingesting flow data from LiveWire to identify real-time cyber threats.
Uncover cyber threats, without decryption, by ingesting flow data from LiveWire to identify real-time cyber threats.

ThreatEye network detection and response solution gives you visibility even if traffic is encrypted.
ThreatEye Lets You:
ThreatEye’s DPD is agnostic to packet contents and is used to create a fingerprint of network flows for profiling and anomaly detection by supporting more than 150 packet traits and behaviors.
Analyze network traffic without multiple passes over the data stream. Machine learning powers our scalable, multi-stage analysis pipeline to process millions of events per second.
Automatic traffic decryption allows you to act on cyber threat intelligence that other solutions miss. DPD eliminates encryption blindness while validating end-to-end encryption compliance.
Save downtime with faster detection through industry-leading real-time detection analysis. ThreatEye processes millions of events per second with a multi-stage analysis pipeline to analyze network traffic without multiple passes over the data stream. Analyzers scale with you to ensure ongoing network security via parallel processing.
ThreatEye’s Deep Packet Dynamics (DPD) creates a historical inventory of traits and behaviors for profiling and fingerprinting, a technique that works equally well with encrypted and unencrypted traffic. Machine learning models identify advanced behavioral threat actor anomalies, including ransomware, phishing, malware, unauthorized remote access (RDP/VPN), reconnaissance, lateral movement, C2, tunneling, hands-on keyboard, and data exfiltration.
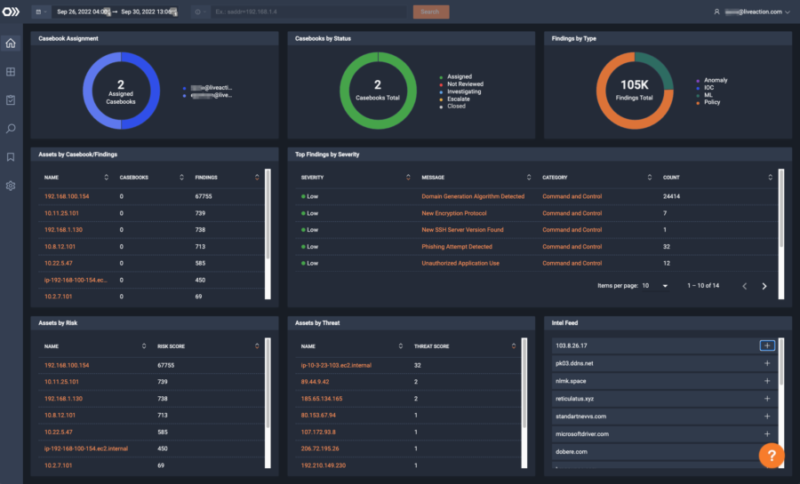
Enable your Network’s Security Operations Center (SOC) by increasing the speed of response. ThreatEye’s multi-stage analysis pipeline correlates and enriches traffic with findings detail, risk scores, and MITRE ATT&CK labeling. With ThreatEye, you can respond in real-time and accelerate triage with integrated packet analysis.
The ThreatEye NDR solution accelerates the threat investigation lifecycle by combining and correlating high-fidelity findings into intuitive and easy-to-deliver standard and custom reports to track the state of an incident, enhancing analyst workflow and efficiency.
Encryption-policy-specific alerting and reporting helps SecOps team with security compliance. The increased adoption of encryption to secure applications calls for a greater need to ensure all platforms conform to the encryption standards of the enterprise.
ThreatEye extracts a rich metadata set of more than 150 packet dynamic features to support threat and anomaly detection, response, hunting, forensics, and compliance validation reporting. Packet dynamic-based metadata focuses on packet traits and behaviors—not contents—to work equally well with encrypted and unencrypted traffic.
“Traditional security tools, like our Intrusion Detection System (IDS), were no longer delivering value. Encryption blocked their ability to analyze most of our traffic.” With a primary concern around threat detection and encryption blind spots, the firm chose ThreatEye because of the way it solves these problems.
– Chief Security Officer
