Without a functional network, most businesses would come to a screeching halt. We look at five traits and best practices of organizations that have pulled off successful network monitoring strategies.
1. Monitor Multiple Data Types
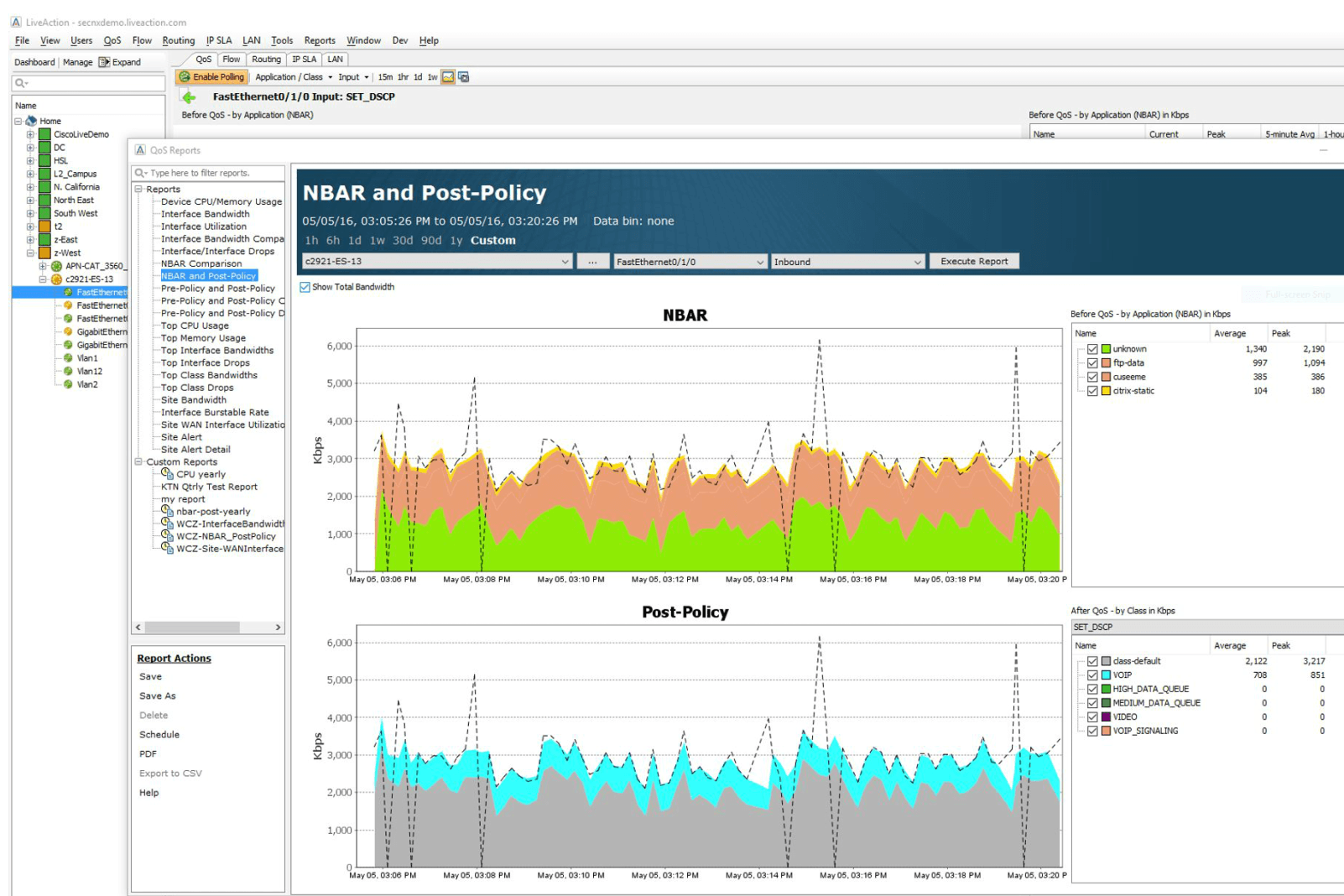
The more the merrier – SNMP, flow, packet, API, and NBAR2 data all contribute to a full picture of network visibility. Each data type brings something unique to the table in monitoring capabilities:
• SNMP allows you to monitor data of interfaces, CPUs, and bandwidth usages of network devices like switches, ports, and routers.
• Flow data collects and summarizes IP traffic to reveal trends in network health over time and point to where events or network saturation occur.
• Packet data takes you from where saturation occurs to the exact application or appliance causing the issue. Packets point to the root cause.
• NBAR2 gives you visibility into HTTP (port 80) and HTTPS (port 443) without the need for taps
• API data monitors transactions during API calls to see if there are performance latency, slow response time, or availability issues during the call
2. Have a Data Retention Policy
Successful network monitoring strategies have a plan of recourse, so when problems do happen, there is an audit trail to trace what occurred. A data retention strategy usually addresses these factors:
• How long to retain different data types
• What format to store the data in
• Where to store it
Having data available for lookback forensics can allow for trend identification over time, help with security issues and maintain compliance requests. Studying historical data logs can influence future policies and procedures used in network monitoring and collection.
3. Keep a Network Map with a Device Inventory
To effectively manage and monitor a network, there cannot be visibility gaps. Every switch, router, port, and endpoint must be physically located and observed live for health and performance issues. While this sort of network inventory mapping can be an arduous manual task, device auto-discovery tools in many network monitoring software platforms create these lists for you. When considering network monitoring tools, inquire if they include a DMS or device management service so you can easily monitor or reset devices remotely.
4. Create a Detailed Escalation Plan
Escalation plans often involve alert prioritization scoring or threat scoring, so alerts falling in the range of different thresholds go to the right predetermined contacts. This helps critical issues like unexpected traffic surges get immediate attention. More benign problems can filter into an investigation queue with a longer response time. A predetermined response plan keeps the organization from having one pool of overwhelming alerts to fish through, minimizes response delay, and creates accountability with the group or pod the alert is specifically assigned to.
5. Automate Wherever Possible
Successful network monitoring strategies focus on efficiency and fast reactions, which means automating where it makes sense. Critical tasks like daily backups, applying security patches and software updates and restarting failed devices, or running weekly reports can free up engineer resources for optimizing network flow paths and planning for future initiatives.
About LiveAction
LiveAction is a network and security monitoring platform that combines several best practices under one easy-to-use monitoring and management solution. From diverse data ingestion, targeted alerting, and custom reports to intelligent packet capture for maximized disc retention space, LiveAction works to continuously innovate its platform to bring the world’s broadest network telemetry solution to NetOps teams everywhere.
Want to learn more about the features rolled into our network monitoring platform? Talk to an expert today.