Contents
Network packets serve as the indisputable carriers of truth. As the backbone of data transmission, these encapsulated pieces of information provide unparalleled insights into the dynamics of our interconnected world. In this document we’ll unravel the reasons behind the assertion that “Network Packets Don’t Lie,” exploring the reliability, transparency, and undeniable authenticity embedded within the language of packets.
01. Unaltered Transmission
Network packets faithfully convey information from source to destination without alteration. Unlike other forms of communication where messages may be susceptible to manipulation or distortion, the integrity of network packets remains intact throughout their journey, ensuring the accuracy of the transmitted data.
02. Raw and Unfiltered Data
Raw and unfiltered data are encapsulated within network packets. Unlike interpreted or processed information, network packets present a direct representation of the digital conversation, offering an unadulterated view of the exchanged bytes. This raw nature makes packet analysis a reliable source for understanding the true nature of communication.
03. Timestamps as Chronological Witnesses
Timestamps within packets are chronological witnesses to digital events. By capturing the exact moment of transmission, timestamps embedded in packets serve as an objective timeline, enabling analysts to reconstruct sequences of events accurately. This temporal transparency is a key factor in validating the authenticity of digital interactions.
04. Packet Headers: A Digital Signature
Packet headers serve as a digital signature of communication. Dive into how headers contain critical information about the source, destination, and type of data being transmitted. This wealth of metadata not only aids in network troubleshooting but also acts as an undeniable testament to the authenticity of the communication.
05. Forensic Value in Packet Payloads
The payload, the actual data being transmitted, provides a rich source of evidence for digital forensic analysis. Whether it’s uncovering security threats or investigating incidents, packet payloads offer an unaltered representation of the digital conversation.
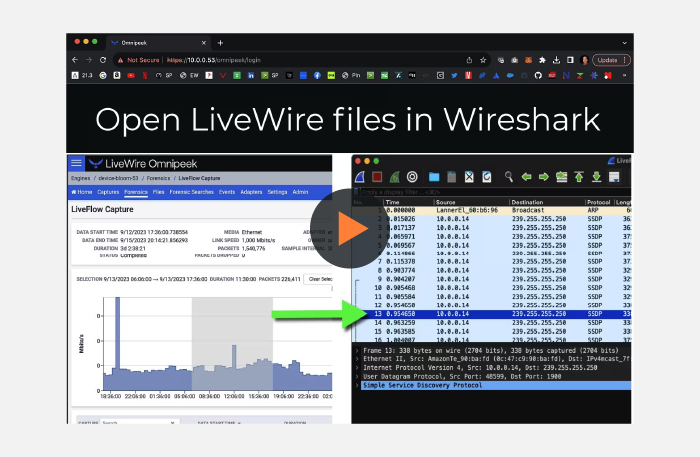
06. Packet Sniffing: Capturing the Truth
Packet sniffing is a means of capturing the truth. By intercepting and analyzing network packets, organizations gain unparalleled visibility into their digital landscape. Discuss how this practice is not about intrusion but about understanding and securing digital communications transparently.
07. Authentication through Network Signatures
Network signatures can serve as a form of authentication. Just as a handwritten signature uniquely identifies an individual, network signatures within packets uniquely identify devices, applications, and communication patterns. This inherent authenticity adds a layer of trust to the information carried within the packets.
Conclusion
In the world of digital communication, where misinformation and manipulation can be prevalent, network packets stand as the bearers of truth. Their raw, unaltered nature, coupled with timestamps, headers, payloads, and network signatures, makes them a reliable and transparent source of information. As organizations navigate the complexities of the digital landscape, the assertion holds true: “Network Packets Don’t Lie,” providing a steadfast foundation for understanding, securing, and optimizing our interconnected world.
About LiveAction®
LiveAction provides end-to-end visibility of network and application performance from a single pane of glass. We provide enterprises with confidence that the network is meeting business objectives, full network visibility for better decisions, and reduced cost to operate the network.