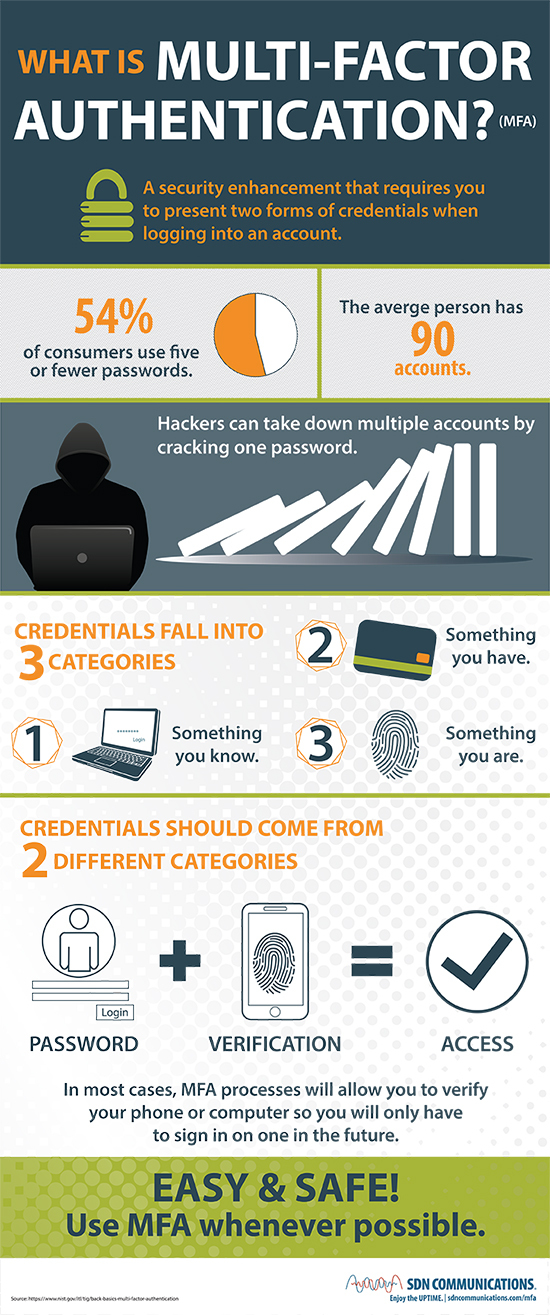
What is MFA?
Multifactor authentication or MFA is a user authentication method that requires 3 or more verifications to gain access to an account, VPN, or application.
How Does MFA Work?
MFA verification methods can include a text message, an email, a QR code, pin number, browser push notifications, security questions, and at least one form of biometric identification like a fingerprint or face scan to gain access. It involves one additional verification step over two-factor authentication (2FA) and two more steps over single-factor authentication (SFA), where you only need a password.
Although it is an additional verification metric, most sites have location-based or time-based factors or automatic device recognition that makes this additional verification step invisible to end-users but an additional hurdle for the attacker attempting to crack it.
Here’s a helpful infographic that simplifies the MFA process:
Why is MFA Important?
MFA is a small change that dramatically reduces attacks. Did you know that Verizon’s 2022 DBIR found that 80% of breaches can be traced back to stolen passwords? The number of stolen credential situations has increased by 30% since 2017, becoming a favorite of attackers for gaining network access with a low bar of entry. These statistics point to what happens when MFA is not implemented. 2FA can be bypassed with phishing, social engineering, rainbow table attacks, and SIM-jacking but the extra effort required with MFA makes most attackers move on to easier targets.
Benefits of MFA and the Consequences of not having it
MFA reduces the success rates and attempts by attackers.
Google’s security blog shared the stunning findings that 95% of bulk phishing attempts and more than 75% of targeted attacks can be resolved by adding MFA.
Without MFA, it’s much easier for hackers to crack your password. They use techniques like brute force, which run automated scripts that attempt letter, symbol, and number combinations to arrive at your password.
It might be easier than you think. Each year NordPass releases a report of the top 200 most common passwords, and there are apparently several people who think alike. Here are the top 10 for 2021
| PASSWORD | TIME TO CRACK IT | COUNT ( # of times used) |
| 123456 | < 1 second | 103,170,552 |
| 123456789 | < 1 second | 46,027,530 |
| 12345 | < 1 second | 32,955,431 |
| qwerty | < 1 second | 22,317,280 |
| password | < 1 second | 20,958,297 |
| 12345678 | < 1 second | 14,745,771 |
| 1111111 | < 1 second | 13,354,149 |
| 123123 | < 1 second | 10,244,398 |
| 1234567890 | < 1 second | 9,646,621 |
| 1234567 | < 1 second | 9,396,813 |
Threat actors also use malware like keylogging and session hijacking to grab passwords and buy lists of credentials off the dark web. According to TechSpot 70% of adults reuse the same password more than once, which means if your password has been in a breach before, it can serve as a valuable access point for additional attacks. To check if any of your passwords have been exposed in a data breach, go to haveibeenpwned.com. Using a password manager makes it easier to create and maintain several unique passwords. There are many free password managers available, including one built into the Google Chrome.
The consequences of not using MFA can be easy to see, even from one account breach. Imagine your Gmail gets hacked. That one access point contains your contacts, your history of conversations, your calendar, and any collaborative documents you have in docs, sheets, or slides and possibly much more.
It is particularly disconcerting that so many large breaches stem from the use of default and/or shared credentials, given the relative ease with which these attacks could be prevented. – Verizon Data Breach Investigation Report
How to Choose an MFA Solution
- Look for a user-friendly tool. If it’s not easy to do, people won’t do it.
- Select a tool that covers all systems and applications that require login to access. Some tools will Nickle and Dime you and make you select certain applications to protect with MFA and leave others unprotected. Get a carte blanche total access solution.
- See what integrations the MFA tool has and try to find one that has integrations that work with all of your critical applications and services
- Test it out! Most MFA solutions offer a 30-day free trial period so you can see what works best in action.
So if I Add MFA, Am I Safe?
MFA is only half the battle, but it’s a battle worth fighting. While ruling out stolen credentials significantly cuts down the chance of a breach, it doesn’t address another common attacker technique, exploits.
Exploiting web applications through unpatched vulnerabilities and other backdoors do not require credentialed access and will need additional security tools to address.
About LiveAction
ThreatEye by LiveAction picks up where MFA stops and can address the cybersecurity space beyond stolen passwords. ThreatEye secures enterprises across on-premise, private, hybrid, public, and multi-cloud environments. next-gen AI-driven NDR platform enriches and correlates data from disparate sources to enable network security analysts to respond in real time. Using advanced fingerprinting techniques, ThreatEye uniquely characterizes the behavior of assets to identify malicious activity. Learn more about ThreatEye and talk to an expert today.