Innovation Driven By ColdWar Anxiety
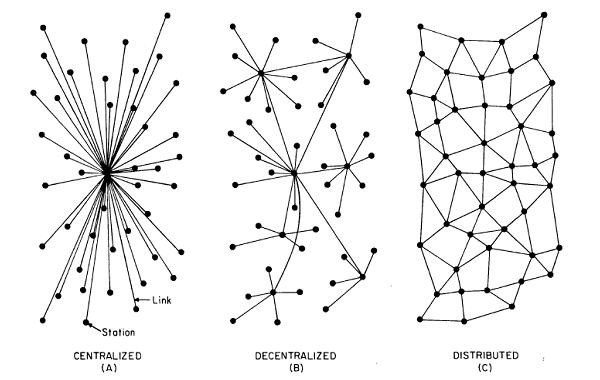
The original model for the internet was based on a centralized network for maximum efficiency and control. But once the ColdWar began, the Department Of Defense (DOD) got nervous about what a centralized network meant for cybersecurity. Network engineer Paul Baran created the concept of a decentralized network in a proposal for the US AirForce.
The idea was that if Russia delivered a cyberattack, but the equipment, devices, and switches were distributed around the network, the attack would not take down the entire network. Traffic could be delivered through alternate paths, and communications would not be crippled.
Despite this early realization that decentralized networks could offer better redundancy, security, and improved network availability, the broader public felt that they specifically were unlikely to be at the receiving end of a Russian cyberattack.
The inconvenience of changing to a new network model was worth the risk of maintaining the status quo. Still, today the more familiar centralized model is the most widely used network on the internet. However, current trends and risk assessments along with an era of indiscriminate and monetized cyber-attacks are tipping the network popularity contest towards decentralized and distributed models.
This post examines why centralized networks have had a decades-long appeal to organizations and what factors and benefits are gaining momentum for decentralized and distributed network transitions.
Let’s first consider the architecture of a centralized network and its advantages.
Centralized Network
A centralized network is characterized by one centralized server or node receiving data requests from peripheral nodes and follows the traditional hub-and-spoke architecture. The central node or server node serves the peripheral nodes, sometimes called the client nodes. All transactions pass through a primary server. This server is the central point of connection between the peripheral nodes. 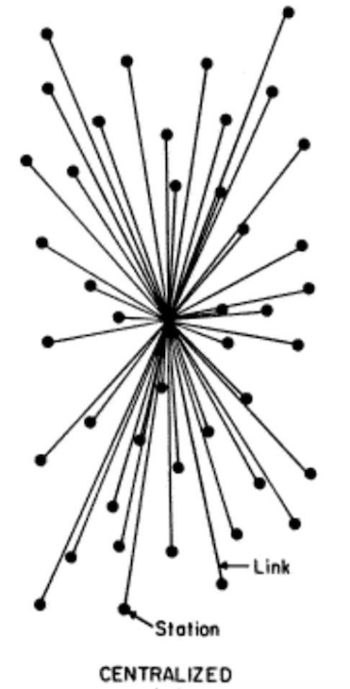
There are many reasons that organizations continue to use centralized networks. This type of network is not complex. It is easy to control and manage. This simplicity comes with several advantages.
Advantages
This structure allows for the greatest control. It is more cost-efficient to centralize IT structures. Centralized networks make reporting, securing, monitoring, and management simple. With less complexity, it is easier to act in unison when making changes or updates. It can scale to an extent, but a single lead server’s capacity can only go so far. This network model will work for small to mid-size organizations as long as they are not experiencing rapid workforce growth or using bandwidth-intensive applications.
Disadvantages
Security
Cybersecurity was not top of mind of organizations until recent years when it became apparent that hackers will target any organization of any size if a known vulnerability can be found on their network. This has realigned priorities for many enterprises who have to acknowledge that centralized networks are easier to hack and harder to recover.
Scalability
Scalability is also a concern. Centralized network models do not scale well. Centralized networks struggle to aggregate and manage increasing volumes of data. Every request must go through a single central server. As the volume of requests increases, bottlenecks build up. With an exponential data increase in just the last few years, organizations are finding they have outgrown this model.
No Middle Ground
Additionally, when a failure does happen, it’s a complete outage. When the lead server fails, it brings down every connection in that network. This level of dependence on network connectivity is a significant business continuity risk.
Maintenance Pain
Maintenance of the server is also a headache. Any maintenance window is guaranteed downtime for the company and often results in delayed patches and updates – leaving networks vulnerable to attack and more willing to run end-of-life hardware rather than deal with the pain of replacing it.
At the Mercy of One Provider
Finally, a centralized network is more likely to rely on a single vendor and in a vendor lock-in situation which leaves the organization helpless to rate hikes, SLA failures, and other service issues.
Decentralized Networks
A Decentralized Network, also called a “Data Mesh” architecture, distributes the control and switching equipment throughout the network to various peer connection points. Each chosen connection point has a separate server that manages the data and information storage for that cluster of nodes. 
Advantages
Resilience
Decentralized Networks have greater resilience. Any connection point can act as a backup server for another, creating fail-safes and redundancy throughout the organization. Each connection point is responsible for its information processing. If one node is hacked, it does not bring down the entire system because only that connection point is compromised.
Agility
Agility is also a hallmark of Decentralized networks. Because the architecture is not concentrated, workloads and shared resources can be distributed over multiple computer nodes instead of just one.
Instead of traveling to a central node to complete a task, data can be sent locally, creating faster accessibility. Other benefits of a decentralized network include faster MTTR. With localized troubleshooting, there is less network to wade through before finding the root cause of an issue.
Decisions can be reached sooner on the procurement and approval side because contract revisions and change considerations are more limited in scope. This opens the door for greater customization of processes and applications that make sense for each location. Organizations can take advantage of new technology more quickly and test its efficacy through individual nodes instead of waiting in a backlogged queue of approvals and hoping for the best. This model is not bound by capacity constraints and is ideal for large enterprises and mid-size enterprises on a growth track.
Disadvantages
The lack of vertical top-down visibility throughout the network can make scaling up or global changes challenging to pull off in unison. It can also be hard to gain oversight and the analytics needed to meet compliance requirements and measure performance.
Distributed Networks
Distributed networks can refer to both location and architecture. Geographically distributed networks are what you see in digital-first companies, with employees who work remotely across the entire organization. There is no question that geographically distributed networks are increasing.
According to a recent study cited by Forbes, 25% of all professional jobs in North America will be remote by the end of 2022, and remote opportunities will continue to increase through 2023.
Architecturally distributed networks have a slightly different meaning. These structures distribute control equally across each node. This is different from decentralized networks with clusters of varying connection points throughout the network. 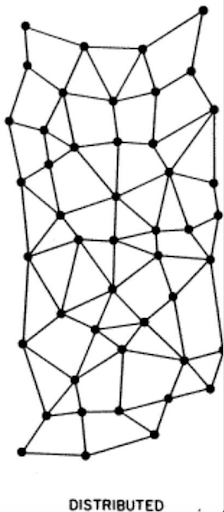
Advantages
Each node is independent and can act as a backup for the other. If a part of the network goes down, the protocol can be redirected through different routes. Like Decentralized networks, distributed networks offer more security, stability, and scalability than centralized networks. Still, unlike decentralized networks that use clusters of smaller “centralized” servers, the control is distributed evenly across each node.
Disadvantages
There is no central router to manage IP addresses, so making any changes in unison can be challenging. It is more expensive and requires more equipment to have distributed power and control at each node. Centralized visibility is an issue making audits or compliance requirements a nightmare.
The Future
Since its inception, centralized networks have dominated the internet, but there is no question that the future is decentralized and distributed infrastructures. The modern enterprise cannot afford the risk of non-redundant network structures and the security vulnerability of having a single point of failure. The future network can manage the influx of data without congestion and stay up when a network issue occurs. The secret to orchestrating these moving and multiplying pieces is enhanced network visibility.
About LiveAction
LiveAction offers the broadest network monitoring and management telemetry in the industry. Whether Centralized, Decentralized or Distributed, LiveAction can provide enhanced visualization for your network infrastructure from WAN edge to core to cloud.
Through LiveNX, LiveWire, and ThreatEyeNV, LiveAction delivers a complete suite of tools that assure your network availability, security, and speed optimization. Request a demo with one of our network experts today.
Want to learn more about the history of all things internet?
Check out our post that dips into the history AI Ethics or read about how network monitoring got its start.


